DATAPK
DATAPK is a specialized product, designed for critical infrastructure objects and critical IT infrastructure security status monitoring, incl. Industrial Control Systems (ICS).
Due to the nature of many industrial processes resulting damage from an ICS security incident may impact human safety and natural environment.
ICS security breach may result in severe technological consequences, such as:
- accidents, resulting in human safety impacts, environmental impacts, and production equipment damage;
- industrial and technological process disruption resulting in financial losses;
- fraud and theft occurring via misuse of the ICS components.
In order to detect security breach preconditions and prevent ICS-related incidents, USSC has developed an Industrial Security Monitoring System (ISMS) based on DATAPK – a specialized product, designed to provide real-time and retrospective ICS security status monitoring and analysis.
DATAPK is based on internal R&D study results in ICS security, state-of-the-art modern technologies, and a deep practical expertise derived from numerous projects.
DATAPK is designed to:
- detect unsanctioned ICS changes and notify the operators;
- discover unprotected ICS assets;
- discover assets with critical vulnerabilities;
- detect vulnerability exploitation attempts;
- log security events and incidents;
- automate compliance status control.
DATAPK advantages:
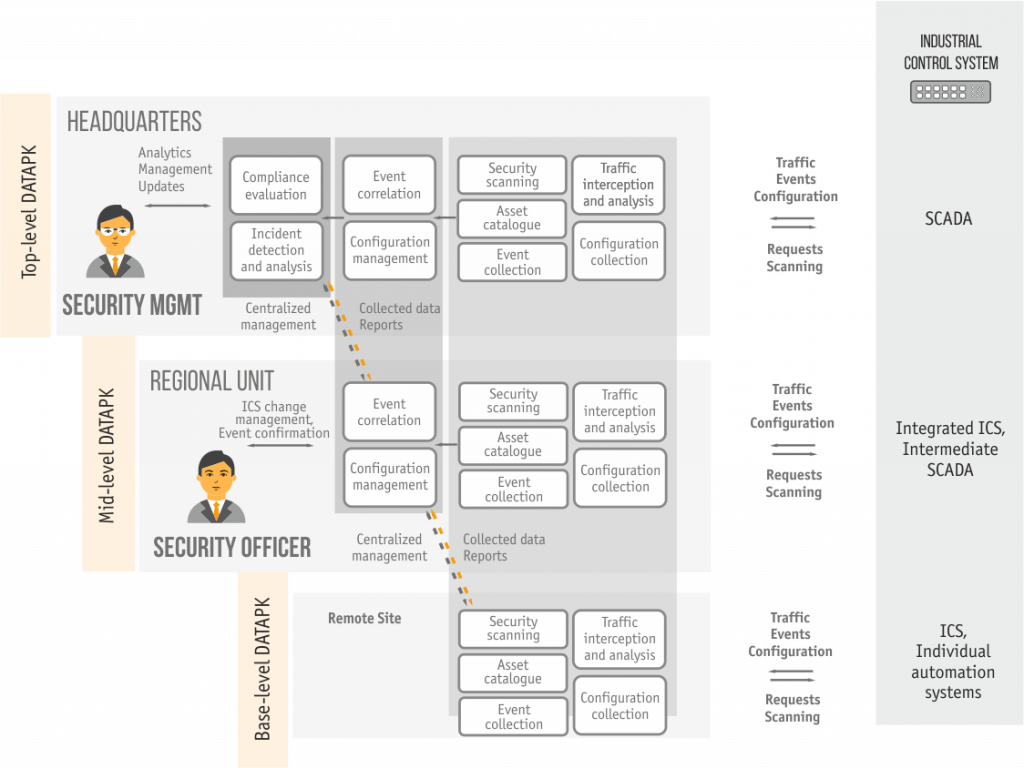
- requires no agent software installation on ICS assets;
- minimum ICS network performance impact;
- several deployment options including industrial appliance;
- various operation modes for different ICS classes and asset types;
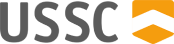
- centralized and local management support;
- external security management system integration;
- hierarchical SIEM integration support.
DATAPK functions:
- Secured assets catalogue: asset discovery and list change monitoring.
- Security events management: collection, normalization and correlation for ICS and security subsystem assets.
- Asset configuration management and anomaly detection.
- ICS vulnerability detection and compliance control for state and enterprise regulations and policies.
DATAPK operation modes:
- Passive monitoring
This mode utilizes unidirectional traffic flow and analysis, having zero impact on the secured ICS.
- Active monitoring
Active monitoring requires bidirectional information exchange, such as event and configuration collection. Active monitoring relies on built-in ICS asset remote access protocols and does not generate additional load on the asset CPU and other resources.
- Vulnerability scanning
Scanning requires active interaction between DATAPK and the secured assets in order to detect vulnerabilities and possible exploits. This mode is recommended for application during ICS maintenance only.